Kelihos Adopts Anti-Analysis Technique
Since the end of April we discovered that Kelihos adopted an anti-analysis functionality. The backdoor detects the presence of the following processes running on a computer that are related to malware analysis tools (network sniffers, debuggers, screen recorders), virtual platforms (VirtualBox) and sandboxes (Sandboxie):
cv.exe
irise.exe
IrisSvc.exe
wireshark.exe
dumpcap.exe
ZxSniffer.exe
Aircrack-ng Gui.exe
observer.exe
tcpdump.exe
WinDump.exe
wspass.exe
Regshot.exe
ollydbg.exe
PEBrowseDbg.exe
windbg.exe
DrvLoader.exe
SymRecv.exe
Syser.exe
apis32.exe
VBoxService.exe
VBoxTray.exe
SbieSvc.exe
SbieCtrl.exe
SandboxieRpcSs.exe
SandboxieDcomLaunch.exe
SUPERAntiSpyware.exe
ERUNT.exe
ERDNT.exe
EtherD.exe
Sniffer.exe
CamtasiaStudio.exe
CamRecorder.exe
vba32arkit.exe
The same verification is done for the registry keys:
SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Wireshark
SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\wireshark.exe
SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Win Sniffer_is1
SOFTWARE\Classes\PEBrowseDotNETProfiler.DotNETProfiler
Software\Microsoft\Windows\CurrentVersion\Explorer\MenuOrder\Start Menu2\Programs\Debugging Tools for Windows (x86)
SYSTEM\CurrentControlSet\Services\SDbgMsg
Software\Microsoft\Windows\CurrentVersion\Explorer\MenuOrder\Start Menu2\Programs\APIS32
SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\APIS32
SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Oracle VM VirtualBox Guest Additions
SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sandboxie
SOFTWARE\SUPERAntiSpyware.com
SOFTWARE\Classes\SUPERAntiSpywareContextMenuExt.SASCon.1
SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ERUNT_is1

Supposedly these lists were partly borrowed from the Simda backdoor.
Kelihos continues preferring Ukrainian servers to download new updates (you can read more about a geographic distribution of the botnet in past
here):
| URL | Country |
|---|---|
| hxxp://178.150.139.157/mod1/zlubob1.exe | |
| hxxp://5.105.69.96/mod2/zlubob1.exe | |
| hxxp://213.111.239.19/online.htm | |
| hxxp://194.44.49.98/mod1/zlubob1.exe |
The downloaded file “zlubob1.exe” is 612 352 bytes (MD5: b4f8a1e28e762567bcf3ade3405259df) and can provide Remote Desktop connection to the attacker via WTS (Windows Terminal Server) API mentioned in the import table.

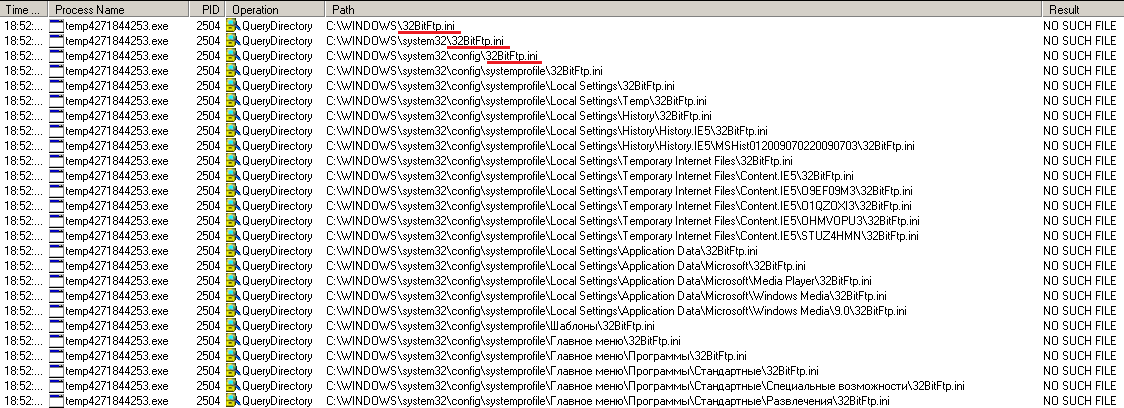
The registry keys enumeration and password files searching is the reason of a high CPU load - 99%:

As we already wrote in the blog it searches for passwords stored in configuration and cache files of FTP clients and Internet browsers:
WISE FTP, IE, Mozilla Firefox, Chrome, Chromium, Bromium, Nichrome, RockMelt, Comodo, ChromePlus, browser.yandex, LeechFTP, Odin, WinFTP, FTPGetter, Estsoft\ALFTP, Staff, Blaze, NetFile, GoFTP, 3D-FTP, EasyFTP, XFTP, BlazeFTP, SiteDesigner, Whisper Technology\FTP Surfer, VanDyke\SecureFX, Fling, NetDrive, FTP Explorer, FTPRush, UltraFXP, AceBIT, Flock\Browser, FTP-Now

We may conclude that the Kelihos botnet is growing again and it has already eaten the biggest piece of botnets pie – 58% in May 2014. The bot has the same thief payload. However, it is armored now with an anti-analysis functionality that will complicate the reversing and debugging a backdoor.

Read also:
Lavasoft Security Bulletin - May 2014: Bot Review.
Share this post:
 Twitter
Twitter