Update on Kelihos Botnet (August 2013)
Part 2. Communication Protocol
We continue observing new modifications of Kelihos and its activity. In this post we will examine the new behavior of a sample caught on 23rd of July (MD5: dbd2f07a60392d2d3ed68c368212ecd4 ).
We reported about new features that were introduced in March, 2013. Now we will highlight the new functionality that has appeared since that time.
Part 1. Installation
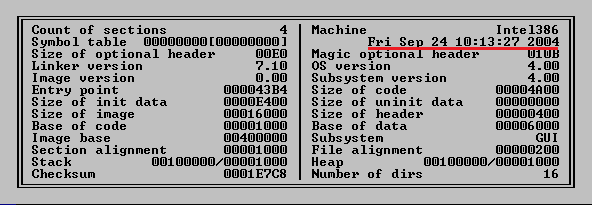
It still has a fake creation date (the unpacked one has a zero date/time stamp):
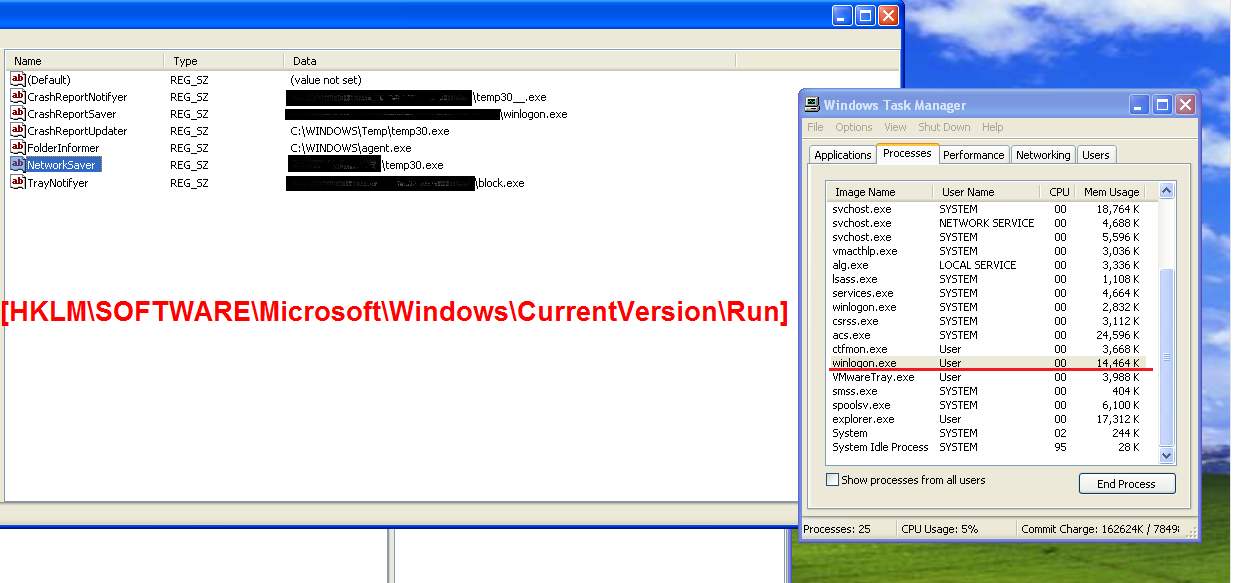
In the registry, “SonyAgent” is no longer used in the Run key. “Sony” labels in other registry keys and .lnk files, seen in older versions, are also no longer used. The backdoor now uses random names from the list in the Run key:
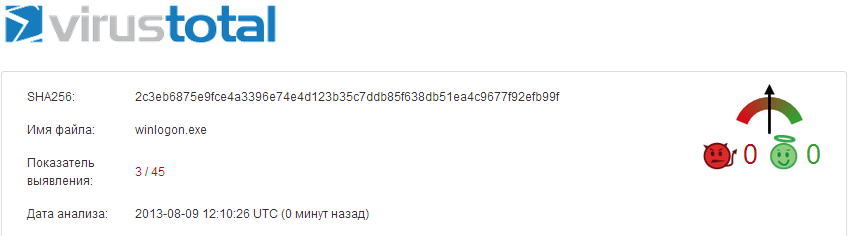
This drop seems to be recently generated and has a very low detection rate by file scanners:
As you can see above, Kelihos uses the file name “winlogon.exe” for the malicious process executed under a user’s account. The trick is that Windows considers this process as a system process and protects it from being terminated even though it is run by “User”.
In general, the Autorun parameter name is constructed from the following words:
| Informer Verifyer Saver Notifyer Checker |
Updater Network Time CrashReport Database |
Icon Desktop Tray Video Media |
The dropped files can be saved under the following names:
| zumodrive zcfgsvc xsd wmpnscfg wmpnetwk wisptis winlogon webscanx vsmon view uptime upgrade update unzip unpack unhide trustedinstaller toaster terraria taskman svchost spoolsv |
smc sidebar services rundll32 rename qttask qbw32 point32 play pdvddxsrv pctspk nwiz nvxdsync nvsvc32 ntvdm nprotect navapsvc naprdmgr mspmspsv mscorsvw msascui mcvsescn |
mcshield mac lucoms lsass launch lame klwtblfs khalmnpr jusched jucheck jqs java isuspm igfxtray iexplore ieuser ielowutil htpatch hkcr hkcmd gearsec fix |
firefox ezsp_px extract explorer em_exec edit dwm download dit defwatch decompile convert ccsetmgr ccevtmgr ccapp block batch avguard ati2evxx alg agent acrord32 |
Part 2. Communication Protocol
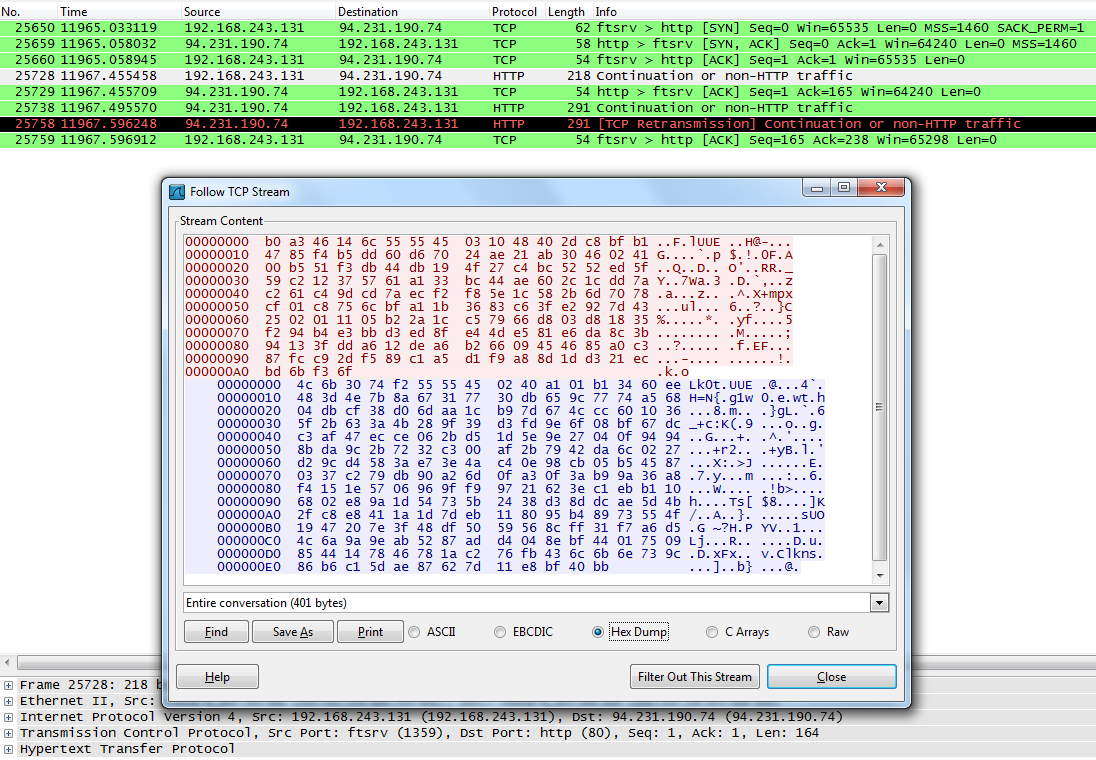
The image below shows a handshake between near peers within the botnet. The list of peer IPs is stored in the backdoor’s body and can be exchanged with peers. The peer handshake looks like as follows:
The latest protocol has been already cracked by Kyle Yang from Fortinet, who reported the protocol encryption at Blackhat 2012. You can read more about utilized cyphers and packet structure here.
After a successful exchange of keys the backdoor can receive the new list of peers, job servers and URL with a fast-flux domain (see the “Fast-flux network” section below) used to download an update of the backdoor like the current sample has:
hxxp://davujuz.com/moon004.exe
The information about peers is stored in the backdoor’s body and it is decrypted after peers made the mentioned above handshake and ready for exchange:
After deserialization of data we can see the list of peer IPs to be sent:
46.118.133.0(:80), 79.164.120.2, 46.119.136.3, 82.211.142.4, 77.236.173.5, 188.231.198.5, 1.172.240.5, 46.35.170.8, 5.178.245.9, 77.234.65.10, 176.124.12.12, 68.184.196.12, 2.93.194.15, 46.237.73.17, 109.86.191.17, 77.122.204.18, 178.218.66.19, 178.150.19.20, 46.160.39.20, 178.172.177.21, 220.137.23.23, 93.79.50.23, 37.115.226.23, 188.0.143.24, 36.239.211.24, 77.123.17.25, 2.95.93.25, 46.211.100.25, 195.114.147.25, 36.224.252.25, 84.234.51.26, 78.139.178.26, 46.149.179.31, 46.118.110.32, 213.159.245.32, 109.207.122.33, 91.243.4.35, 1.173.243.36, 92.245.73.37, 109.162.115.37, 213.110.138.37, 27.3.169.37, 93.178.216.37, 37.229.56.38, 130.204.64.39, 61.70.39.40, 93.77.106.41, 94.112.200.41, 46.185.42.42, 93.79.57.43, 115.252.166.43, 31.128.186.43, 114.38.191.44, 1.169.121.45, 14.99.162.45, 220.138.176.45, 112.139.167.48, 217.196.170.50, 94.230.201.52, 119.32.4.53, 202.142.119.54, 93.79.231.55, 176.8.165.56, 31.133.39.58, 213.240.219.59, 46.118.150.61, 94.154.39.63, 1.173.208.65, 94.240.179.67, 109.87.127.68, 109.86.180.69, 46.251.67.70, 31.193.94.72, 61.82.197.72, 118.168.178.74, 188.242.51.78, 176.8.192.78, 182.234.213.78, 93.114.144.79, 130.206.162.79, 87.118.179.79, 223.19.197.81, 188.190.5.82, 109.201.99.83, 188.242.252.83, 176.114.178.85, 188.241.29.86, 129.15.40.86, 27.4.194.87, 79.135.211.87, 109.184.13.89, 79.135.210.90, 219.71.14.92, 178.90.39.94, 46.119.211.96, 59.120.2.97, 116.193.129.97, 176.121.238.97, 213.216.33.98, 118.232.194.98, 182.233.187.101, 46.72.233.101, 46.211.216.102, 125.224.126.103, 111.252.233.103, 46.250.99.105, 114.24.141.105, 31.170.142.105, 159.224.40.106, 46.150.92.106, 37.221.142.107, 32.64.90.108, 5.248.25.109, 46.119.83.109, 92.243.118.109, 114.47.194.109, 176.122.250.111, 101.2.189.112, 46.160.42.113, 109.162.42.115, 178.66.210.115, 77.120.160.116, 109.86.27.117, 79.110.131.117, 114.46.177.117, 134.17.83.119, 117.208.1.120, 46.160.10.121, 109.86.23.121, 5.104.57.121, 176.114.143.122, 77.70.87.124, 93.78.16.125, 77.122.77.126, 141.170.249.126, 140.130.19.127, 91.204.39.128, 95.87.51.130, 114.37.52.130, 89.137.128.130, 5.200.215.131, 195.96.245.131, 77.122.120.133, 176.113.243.134, 31.131.68.135, 159.224.5.142, 62.245.38.142, 5.105.87.142, 46.250.126.144, 93.79.93.145, 5.248.4.146, 109.191.30.146, 31.46.52.147, 123.110.25.148, 151.249.103.148, 76.186.197.150, 218.35.231.151, 27.3.35.153, 95.24.239.153, 46.211.117.154, 176.98.12.155, 46.118.90.155, 151.237.83.156, 91.246.232.159, 178.137.217.162, 89.43.190.164, 85.217.246.164, 188.129.254.164, 93.77.65.168, 46.241.2.169, 195.114.148.169, 117.200.191.172, 49.206.93.173, 188.173.87.174, 111.92.105.174, 85.186.112.174, 117.204.247.174, 46.211.41.176, 46.46.87.176, 5.248.150.178, 1.173.61.179, 115.240.218.181, 109.86.110.188, 58.176.15.190, 178.151.243.190, 94.137.58.191, 93.185.218.191, 14.96.115.192, 91.149.155.193, 91.147.225.193, 94.153.62.194, 178.168.32.196, 123.240.92.197, 89.215.104.198, 46.211.106.199, 111.243.175.202, 109.86.238.202, 114.45.70.203, 213.88.74.205, 94.244.43.206, 115.242.239.206, 1.170.84.207, 151.0.14.210, 46.185.121.211, 77.236.171.211, 27.6.9.213, 93.185.219.213, 159.224.68.215, 94.230.117.216, 176.73.199.217, 124.125.237.217, 77.121.242.217, 89.22.248.217, 91.241.203.219, 178.151.179.220, 85.130.63.221, 42.201.131.221, 93.100.187.221, 188.213.86.222, 61.57.121.222, 188.138.223.222, 78.97.55.224, 95.83.72.224, 109.162.86.226, 220.136.219.226, 46.118.3.228, 202.59.186.228, 213.110.64.229, 77.123.43.230, 70.45.52.230, 175.111.40.232, 175.100.158.233, 93.78.80.235, 217.117.189.235, 109.86.122.237, 130.255.132.237, 31.133.46.238, 89.20.110.238, 95.105.80.241, 1.175.173.242, 58.5.38.243, 58.97.251.243, 31.43.134.246, 109.87.254.247, 190.120.156.248, 117.220.252.248, 118.170.12.253, 46.49.47.254, 2.190.85.255, 46.211.112.255
Another peer (85.130.63.221) replies with its own peer list:
93.79.51.37(:80), 92.52.181.18, 46.250.0.19, 5.227.135.190, 61.230.142.190, 182.235.161.6, 77.123.45.125, 109.108.69.135, 121.152.86.135, 176.106.211.135, 178.74.223.58, 77.120.142.43, 118.233.148.241, 223.223.153.241, 190.185.164.241, 46.150.84.242, 93.78.115.242, 212.107.231.243, 42.147.66.197, 93.78.158.4, 213.184.247.69, 115.187.35.216, 61.57.83.157, 203.213.166.28, 78.30.250.61, 182.21.29.178, 89.45.153.178, 93.78.69.179, 109.87.12.75, 201.225.70.75, 82.245.151.133, 46.250.16.135, 46.250.18.135, 193.19.134.54, 178.150.244.54, 46.211.23.200, 88.196.131.200, 5.228.137.200, 85.67.177.200, 128.97.122.201, 125.58.102.50, 195.140.229.53, 176.240.46.121, 180.11.51.121, 188.209.246.119, 106.1.25.120, 109.200.236.4, 77.122.174.56, 36.227.11.57, 118.170.240.239, 160.75.9.240, 77.122.72.240, 94.230.200.240, 77.122.183.28, 195.24.155.245, 93.79.70.247, 122.121.198.249, 2.133.231.75, 78.90.112.30, 94.230.201.36, 202.83.44.84, 62.243.91.153, 46.250.24.154, 77.122.55.95, 77.120.154.119, 37.112.160.119, 123.216.163.119, 176.8.235.143, 93.77.241.53, 178.83.11.54, 178.141.114.141, 49.205.157.103, 218.191.134.7, 219.68.178.206, 37.229.233.209, 37.233.47.210, 123.110.64.187, 178.137.79.152, 213.137.43.54, 79.169.26.67, 37.229.182.82, 219.68.168.107, 5.79.194.107, 94.253.42.164, 188.231.173.6, 123.241.36.47, 62.245.123.160, 109.162.111.161, 109.87.24.162, 93.78.96.162, 37.57.48.19, 176.74.95.3, 37.229.125.6, 109.87.83.108, 221.152.167.108, 188.190.12.225, 176.115.150.162, 91.105.58.164, 93.89.218.108, 37.229.6.109, 14.99.241.253, 94.190.79.4, 77.122.196.210, 46.219.28.120, 84.224.16.121, 89.43.246.25, 186.237.77.114, 77.122.95.250, 36.239.214.250, 93.78.189.252, 178.218.105.253, 117.240.116.254, 219.70.253.51, 178.172.196.221, 92.114.254.221, 87.97.55.222, 89.185.12.100, 78.97.53.234, 77.121.47.188, 59.105.191.132, 195.211.190.210, 93.187.200.210, 111.184.61.211, 109.87.209.52, 27.4.101.214, 219.70.155.215, 123.193.10.22, 46.241.53.115, 159.224.5.60, 125.4.213.146, 220.132.120.225, 130.204.90.220, 46.118.99.32, 46.149.177.150, 91.210.54.170, 93.77.79.1, 115.252.167.199, 5.100.93.136, 188.130.200.166, 95.69.255.97, 188.230.64.226, 89.185.30.50, 93.77.123.151, 123.240.88.152, 31.130.90.138, 188.129.218.87, 77.122.164.173, 93.114.241.128, 178.172.242.198, 46.35.227.199, 46.211.76.127, 178.158.72.179, 188.129.243.106, 178.137.47.64, 114.38.20.35, 176.111.189.39, 46.33.55.77, 89.228.126.39, 31.135.42.95, 101.1.84.221, 109.191.218.132, 93.77.254.169, 218.216.209.77, 114.46.254.166, 112.105.197.204, 95.69.142.93, 114.27.158.155, 88.135.81.154, 202.142.124.203, 79.110.139.52, 93.79.217.231, 178.44.173.39, 178.137.187.59, 5.53.216.7, 91.124.190.76, 93.77.103.167, 93.77.53.173, 176.73.205.27, 141.138.126.128, 60.198.112.3, 1.170.177.8, 78.96.13.101, 178.137.98.175, 178.65.127.176, 42.83.30.231, 95.65.80.117, 89.76.144.201, 87.242.22.79, 178.137.177.125, 61.192.122.202, 117.201.23.155, 159.224.238.166, 176.8.9.32, 178.150.185.114, 95.76.205.223, 37.115.79.18, 217.30.202.26, 188.133.205.167, 123.238.235.106, 99.229.162.127, 5.1.20.192, 106.1.39.18, 83.246.151.18, 176.8.17.76, 176.104.172.4, 91.219.62.29, 124.125.238.131, 31.28.242.233, 49.206.148.24, 27.127.152.139, 91.203.15.84, 109.229.189.86, 188.241.218.87, 46.118.67.127, 183.83.78.6, 80.64.93.192, 178.150.25.22, 77.70.71.77, 93.78.199.128, 46.119.201.129, 99.33.193.187, 109.171.31.188, 218.220.225.189, 46.211.48.184, 5.248.171.184, 212.77.129.140, 95.69.166.27, 193.106.223.38, 64.183.20.82, 46.118.170.39, 109.227.212.99, 58.114.150.52, 86.122.247.201, 178.150.159.117, 37.229.102.234, 85.186.165.224, 46.186.91.61, 111.91.48.204, 46.119.254.204, 46.119.246.230, 213.111.209.237, 178.72.74.24, 46.233.35.177, 46.173.111.7, 119.194.106.139, 210.255.207.93, 93.116.84.39, 93.115.53.173, 178.151.76.123, 46.72.203.28
And job servers’ data:
193.105.134.89:80
193.105.134.189:80
78.83.177.243:80
78.83.177.250:80
89.45.14.47:80
89.45.14.49:80
Those IPs have been changing slightly and can be considered as a criterion of successful botnet operation. All job servers are up currently. Although they hide themselves from discovery by blocking ICMP requests it is possible to trace running services by nmap:
Also the peer sent URL to download an update:
hxxp://buv.makgivus.ru/setup2.exe
During July 2013, we detected the following samples that downloaded updates using the links from the table below:
| Sample | Update URL |
| ba8b19b7097ad7ce52db0d487b285ff4 83783b9836a592327de7f9aafd687f40 29226715e0553d9ae2bda39a63933454 0f783b56c2d9b75774290e15d0211ad0 053e8a2948100cda5d48458bcd031e76 38b1fdd77e03c9596a33a773b4aecdc6 ea3c9f1c3587d4fe44ae5ee8eb6c5fc7 ad5178dac3332320513bf735457132f5 9018ebea024496e3c3866b6ee6df98ad 3c248524b9b0903cc5355c41d90f514b 3e04c8d29b822fb5e66c378e5d53240f 63322dad4c7b2b4f9dc28ccb4a8de5c8 162369e43c6587d923b211dd9d219771 1498185ef20c7f1dfe6af87ccfd9e756 90cf2f5fc3ec4dd545ef0b1d549b99d2 25ad9e8feba70fd5327340cf1a320c00 2122ba6ca8a827c0d81f07b025137203 a3e203bbd0587aaade43c3ee49b51b50 a3e203bbd0587aaade43c3ee49b51b50 d42214d707b7f5a41a5db816ec917885 1e88f3c60c8344edf98f2e0b6caf4813 49e8de14cc017fbc467c66aa3cd094f2 1402e0e9962382a3ebddc510a0fcb125 7a080805bb74aeffa9ec2be5731f414b 101ee5c2f7ab774669888895b2c8e08e 95ed27f664b6781cabeb1ecf28284769 97c51a6904315219625ec4e1a5829ea4 795c4f8171e65a00c690730c3087cb75 e22fabe32b3f1d60db917b4b859d78fd 383c43417d572974e108881121be69de 15cbadb43d5c22c67ce910c4c1877a87 fd0a618b04ecf91b873bc90c8c9e5eed b634ac208f3e8a9e571f27265111bfbc bd6cf5ddb52659cfda52b86a0349146d e204957c88be001b21a94a7a210bbaa0 ef4d17424383c361a6df172467680ec6 f1844e00b20e74a93be7199c8bb9775c e0bb47057c5e2ccf87da9e2ae595bf15 911c2e7525d4ce9e7aca71d0a716c714 e65fc1893cb8c823092d14cd04c7f026 c5b9d20e639b874c00afbd2b37f01a78 f39953abee078a80a292b5ce77d76afe 94c76265a10205d72afed979e3d737a2 e6185c3d3ac5760fb2a873675378bc3e dee9c4b7c1b0e8ae2db63ea1fe2fa135 f0f815b986792bd85838e22f421b9a8a f3110be215bc3ae7308f148763a8a532 2f1017e40be5d35e01ce57ac22961332 3f83f43cda515c36fc22a91e48707733 29dbc4f0770c93c66278b66eb7f3ed97 29dbc4f0770c93c66278b66eb7f3ed97 1b57bd973a67391939e833b9cb5ad314 f99b068f44bb3d84fef229bb86f5168c ffc674969023c2ff3282a5d3ab3b4e4e 8ede96cb5fc09ce31f564417308d0205 783263c5664e0949341a82d7b3ef140c a71ccd25c9c0154686fc0eb595e19c96 a41c8b97c1675e8b8db2c9a1ab17d0e6 e23f9872d2f4267af6680197091fbc03 ed273f01b281336a53e87688002b6691 3ef578fd60b851e0dfb2e26d237ff2b7 45e3113359f8a978cf8c3dc886d01b9e 688749a87e6485dc4919a4d1720a0ca2 b69de066260b390420b76c93a8c55c18 365257526bb804562a81cf32fb686d25 e0b6e205d8c59ca62cbbf1441ab43e0a e1e863c712903178d0527d136fab3652 e0411f53e4b2d2f99c7a9b9e05ec6e48 ecb4369f2c43421eb72105dce378a3f3 075972138be823d3d56292c980060e1b e6167c2c02b3c010b8a720b301ca4f1d 12d6c074c606d7cf97d0fbae32560e30 683952618f49e8833f04b06703c3297f ff46167558f2f13781a79a0e02ce39fa c65cca52661ecb12f61250507c735972 be027475525ea98546809672dcfc98b5 bf0e70ee6ae07f35a07655c01a77238b c52e70c9042ea0110b4de0a59f12a56d a14c1c104b2d47afbb3daa61fe5e035e 76f14db10627c2ad1753a9a53a06da70 9b6a2f220212206a5927a0e1b78748aa 7aae4286ab888b2b74ded4cd2439c14e a4d3c58cd2930d42e70229abec468ae0 7914fcc446c02d6ddd7aa784511b858d 8d1d682f628dc59cb033597b72ae2c16 c1723c53940e660c6ece29a655f0733a 1c5da22043a11a1e38282e3bdd7a868c f43a5c07c00b1bd9343664cea521271d 8b49dc65e496c9c7ac3220f016ff9759 a9dd00aab58563bb345b74743e934cfb 0c0a73194cc0664e4d4110a7f703b768 c705acabba6e29b0fb4b9a98cc21f33d c210d6937df13ea982f7163d4f1f72f9 3e5278d3d42a2b91cb96edf2bb249149 f747e0364f401ff76c40fe0ee9defb17 5e37b34e25e5705f11d846a6e2f6609c 047b29f03c5d9d78b72d38ca3c56483d 262e1d1ce354c35769951c1bd0a034eb |
hxxp://bawoxgud.ru/angrim2.exe hxxp://axgyzaws.walqewuq.ru/install.exe hxxp://lymimnib.ru/angrim2.exe hxxp://hipahsah.ru/angrim2.exe hxxp://oktizsez.ru/rasta01.exe hxxp://sisvizub.ru/rasta01.exe hxxp://hipahsah.ru/angrim2.exe hxxp://bawoxgud.ru/rasta01.exe hxxp://fprufy.uphinjaq.ru/install.exe hxxp://bawoxgud.ru/rasta01.exe hxxp://lymimnib.ru/rasta01.exe hxxp://nacwoman.ru/rasta01.exe hxxp://dfw.ollopdub.ru/install.exe hxxp://c6ri.sodkanxo.ru/install.exe hxxp://xoqhozaz.ru/rasta01.exe hxxp://nacwoman.ru/rasta01.exe hxxp://bawoxgud.ru/rasta01.exe hxxp://lymimnib.ru/rasta01.exe hxxp://bljd2.aggaxsef.ru/calc.exe hxxp://acaqizwy.ru/rasta01.exe hxxp://hipahsah.ru/rasta01.exe hxxp://acaqizwy.ru/rasta01.exe hxxp://talozzum.ru/angrim2.exe hxxp://oktizsez.ru/rasta01.exe hxxp://lymimnib.ru/ballsof.exe hxxp://hipahsah.ru/rasta01.exe hxxp://acaqizwy.ru/rasta01.exe hxxp://acaqizwy.ru/rasta01.exe hxxp://acaqizwy.ru/rasta01.exe hxxp://sapigrys.ru/angrim2.exe hxxp://acaqizwy.ru/rasta01.exe hxxp://c2liu.adtyuhuz.ru/calc.exe hxxp://sisvizub.ru/rasta01.exe hxxp://sisvizub.ru/rasta01.exe hxxp://gucqipga.ru/rasta01.exe hxxp://cimmitic.ru/rasta01.exe hxxp://pywudcoz.ru/rasta01.exe hxxp://tosahrux.ru/rasta01.exe hxxp://cimmitic.ru/rasta01.exe hxxp://cimmitic.ru/rasta01.exe hxxp://kykywpik.ru/rasta01.exe hxxp://libcikak.ru/rasta01.exe hxxp://sapigrys.ru/rasta01.exe hxxp://kosnutef.ru/rasta01.exe hxxp://aggaxsef.ru/rasta01.exe hxxp://gucqipga.ru/rasta01.exe hxxp://cyrkapov.ru/rasta01.exe hxxp://buv.makgivus.ru/setup2.exe hxxp://buv.makgivus.ru/setup2.exe hxxp://tovledif.ru/rasta01.exe hxxp://a5epa.hatnuwti.ru/calc.exe hxxp://jyuhysdo.ru/rasta01.exe hxxp://hupjiwuc.ru/rasta01.exe hxxp://xodbiden.ru/rasta01.exe hxxp://hocodmiz.ru/rasta01.exe hxxp://xatzyjha.ru/rasta01.exe hxxp://pojmizaj.ru/rasta01.exe hxxp://rysdebyd.ru/rasta01.exe hxxp://niskixaj.ru/rasta01.exe hxxp://pojmizaj.ru/rasta01.exe hxxp://tovledif.ru/rasta01.exe hxxp://kekhuhfi.ru/rasta01.exe hxxp://wetusror.ru/rasta01.exe hxxp://zuqsiseh.ru/rasta01.exe hxxp://caxbeqyv.ru/rasta01.exe hxxp://confikja.ru/cuper01.exe hxxp://ydhicdor.ru/rasta01.exe hxxp://buv.makgivus.ru/setup2.exe hxxp://ybtoptag.ru/userid2.exe hxxp://mihumcuf.ru/b0ber02.exe hxxp://wepeftum.ru/rasta01.exe hxxp://vybtesox.ru/rasta01.exe hxxp://possyjok.ru/rasta01.exe hxxp://mucemaub.ru/inkr001.exe hxxp://tovledif.ru/angrim2.exe hxxp://higrikpy.ru/rasta01.exe hxxp://dofefdek.ru/rasta01.exe hxxp://mihumcuf.ru/rasta01.exe hxxp://werzosup.ru/rasta01.exe hxxp://berjenaj.ru/rasta01.exe hxxp://cahuzwup.ru/rasta01.exe hxxp://hulizzep.ru/keybex4.exe hxxp://buv.makgivus.ru/setup2.exe hxxp://qeisybyg.ru/userid2.exe hxxp://buv.makgivus.ru/setup2.exe hxxp://lumeiwyn.ru/rasta01.exe hxxp://sipzovic.ru/keybex4.exe hxxp://susvarly.ru/cuper01.exe hxxp://sojouvyc.ru/cuper01.exe hxxp://tofhermi.ru/cuper01.exe hxxp://oznoznes.ru/cuper01.exe hxxp://zuqsiseh.ru/traff01.exe hxxp://ditojtap.ru/rasta01.exe hxxp://qabadpix.ru/rasta01.exe hxxp://afau.gajkukuc.ru/calc.exe hxxp://ywhyiwdy.ru/rasta01.exe hxxp://uwpaytnu.ru/cuper01.exe hxxp://ditojtap.ru/rasta01.exe |
Part 3. Spreading via USB
The Backdoor copies itself to the root folder of all the removable drives with the following name:
X:\%name from the list%.exe
Where the name can be as follows:
password
screensaver
click
installer
hentai
run
porn
game
To launch the malicious file on the removable drive, the Trojan exploits the CVE-2010-2568 vulnerability. The vulnerability is located in the "CtrlExtIconBase::_GetIconLocationW" function of the "shell32.dll" library which allows launching a malicious file on the removable drive.
The backdoor creates a lnk file:
X:\Shortcut to %file name from the list%.lnk
Part 4. Dummy User-Agents
The list of user-agents used to construct http requests has been enhanced from 28 (in March) to 47 records and now looks as follows:
Mozilla/5.0 (Windows NT 5.1) Gecko/20100101 Firefox/14.0 Opera/12.0
Opera/9.80 (Windows NT 5.1; U; zh-sg) Presto/2.9.181 Version/12.00
Opera/9.80 (Windows NT 6.1; U; es-ES) Presto/2.9.181 Version/12.00
Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.0) Opera 12.14
Mozilla/5.0 (Windows NT 6.0; rv:2.0) Gecko/20100101 Firefox/4.0 Opera 12.14
Opera/9.80 (Windows NT 6.0) Presto/2.12.388 Version/12.14
Mozilla/5.0 (Macintosh; U; Intel Mac OS X 10_6_7; da-dk) AppleWebKit/533.21.1 (KHTML, like Gecko) Version/5.0.5 Safari/533.21.1
Mozilla/5.0 (Macintosh; U; Intel Mac OS X 10_6_8; de-at) AppleWebKit/533.21.1 (KHTML, like Gecko) Version/5.0.5 Safari/533.21.1
Mozilla/5.0 (iPad; CPU OS 5_1 like Mac OS X) AppleWebKit/534.46 (KHTML, like Gecko ) Version/5.1 Mobile/9B176 Safari/7534.48.3
Mozilla/5.0 (Macintosh; Intel Mac OS X 10_7_3) AppleWebKit/534.55.3 (KHTML, like Gecko) Version/5.1.3 Safari/534.53.10
Mozilla/5.0 (Macintosh; Intel Mac OS X 10_6_8) AppleWebKit/537.13+ (KHTML, like Gecko) Version/5.1.7 Safari/534.57.2
Mozilla/5.0 (iPad; CPU OS 6_0 like Mac OS X) AppleWebKit/536.26 (KHTML, like Gecko) Version/6.0 Mobile/10A5355d Safari/8536.25
Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0; chromeframe/12.0.742.112)
Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0; SLCC2; Media Center PC 6.0; InfoPath.3; MS-RTC LM 8; Zune 4.7)
Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 7.1; Trident/5.0)
Mozilla/5.0 (Windows; U; MSIE 9.0; Windows NT 9.0; en-US)
Mozilla/1.22 (compatible; MSIE 10.0; Windows 3.1)
Mozilla/4.0 (compatible; MSIE 10.0; Windows NT 6.1; Trident/5.0)
Mozilla/5.0 (compatible; MSIE 10.0; Macintosh; Intel Mac OS X 10_7_3; Trident/6.0)
Mozilla/5.0 (compatible; MSIE 10.0; Windows NT 6.1; Trident/4.0; InfoPath.2; SV1; .NET CLR 2.0.50727; WOW64)
Mozilla/5.0 (compatible; MSIE 10.0; Windows NT 6.1; Trident/5.0)
Mozilla/5.0 (compatible; MSIE 10.0; Windows NT 6.1; Trident/6.0)
Mozilla/5.0 (compatible; MSIE 10.0; Windows NT 6.1; WOW64; Trident/6.0)
Mozilla/5.0 (Macintosh; Intel Mac OS X 10.8; rv:21.0) Gecko/20100101 Firefox/21.0
Mozilla/5.0 (Windows NT 5.0; rv:21.0) Gecko/20100101 Firefox/21.0
Mozilla/5.0 (Windows NT 5.1; rv:21.0) Gecko/20100101 Firefox/21.0
Mozilla/5.0 (Windows NT 5.1; rv:21.0) Gecko/20130331 Firefox/21.0
Mozilla/5.0 (Windows NT 5.1; rv:21.0) Gecko/20130401 Firefox/21.0
Mozilla/5.0 (Windows NT 6.1; rv:21.0) Gecko/20100101 Firefox/21.0
Mozilla/5.0 (Windows NT 6.1; rv:21.0) Gecko/20130328 Firefox/21.0
Mozilla/5.0 (Windows NT 6.1; rv:21.0) Gecko/20130401 Firefox/21.0
Mozilla/5.0 (Windows NT 6.1; WOW64; rv:21.0) Gecko/20100101 Firefox/21.0
Mozilla/5.0 (Windows NT 6.1; WOW64; rv:21.0) Gecko/20130330 Firefox/21.0
Mozilla/5.0 (Windows NT 6.1; WOW64; rv:21.0) Gecko/20130331 Firefox/21.0
Mozilla/5.0 (Windows NT 6.1; WOW64; rv:21.0) Gecko/20130401 Firefox/21.0
Mozilla/5.0 (Windows NT 6.2; rv:21.0) Gecko/20130326 Firefox/21.0
Mozilla/5.0 (X11; Linux i686; rv:21.0) Gecko/20100101 Firefox/21.0
Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:21.0) Gecko/20100101 Firefox/21.0
Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:21.0) Gecko/20130331 Firefox/21.0
Mozilla/5.0 (Windows NT 6.1; rv:22.0) Gecko/20130405 Firefox/22.0
Mozilla/5.0 (Windows NT 6.1; Win64; x64; rv:22.0) Gecko/20130328 Firefox/22.0
Mozilla/5.0 (Windows NT 6.2) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/28.0.1464.0 Safari/537.36
Mozilla/5.0 (Windows NT 6.2) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/28.0.1467.0 Safari/537.36
Mozilla/5.0 (Windows NT 6.1) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/28.0.1468.0 Safari/537.36
Mozilla/5.0 (Windows NT 6.2; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/29.0.1547.2 Safari/537.36
Mozilla/5.0 (compatible; MSIE 9.0; AOL 9.7; AOLBuild 4343.19; Windows NT 6.1; WOW64; Trident/5.0; FunWebProducts)
Mozilla/5.0 (compatible; MSIE 8.0; Windows NT 6.0; Trident/4.0; Acoo Browser 1.98.744; .NET CLR 3.5.30729)
Part 5. Passwords Stealer
The backdoor now, additionally, searches for credentials from the following applications:
Cyberduck
FreshFTP
FTPShell
Global Downloader
Notepad++
TFTPInfo
MyFTP
Sherrod
NovaFTP
CoolNovo
The complete list of attacked applications from where stored passwords are stolen is as follows:
| FAR Manager FTP Windows/Total Commander FlashFXP BulletProof TurboFTP WebSitePublisher SoftX FTP Client Directory Opus LeapFTP WinSCP 32bit FTP FTP Control SecureFX BitKinex CuteFTP |
Core FTP WebDrive Classic FTP NetDrive FileZilla FTP Explorer SmartFTP FreeFTP/DirectFTP FTPRush Frigate3 ExpanDrive WISE Leech Wisper/Surfer FTPGetter |
Blaze NetFile 3DFTP XFTP Robo Linas CyberDuck Putty Global Downloader Notepad++ CoffeeCup TFTPInfo Nexus MyFTP Sherrod ALFTP |
Yandex Mozilla Firefox IE Chrome Chromium ChromePlus Bromium Nichrome Comodo Rockmelt CoolNovo Deluxe Staff NovaFTP AceBIT FFFTP |
Part 6. Fast-flux Network
We analyzed the following fast-flux domain name “ditojtap.ru” and counted 4543 IP addresses associated with it. The map looks pretty similar to the one we had in March 2013. The top of the chart, as usual, is occupied by Ukraine with 47% of proxy-bots serving the botnet.
Conclusions
• The Kelihos botnet is still in operation despite all the takedowns in the past. This is attributable to a sustainable P2P architecture.
• All job servers are up and running.
• It now tracks even more software agents to steal user’s credentials.
• To hide itself in a more efficient way the backdoor started using random names for files and registry parameters. The number of dummy user-agents has been increased from 28 to 47.